Introduction
In the landscape of email marketing, the emergence of bot-clicks poses a nuanced challenge for senders, ranging from a minor inconvenience to a significant disruption. Bots navigate the links within emails, leaving behind a trail of clicks that directly impact metric reporting. But why do these bots exist, and what purpose do they serve beyond complicating the lives of email senders? This blog aims to unravel this hidden thread and provide insights to help you find them in your own data.
What are they?
At risk of sounding obvious, a “bot-click” is just that: a click generated by a bot. A bot can be any type of computer program that performs automatic operations on behalf of another user or system. In an email ecosystem, these robots read email to assess the validity and trustworthiness of the content. Part of this process may be following the links. As these robots do their work, they generate “clicks” on the links in your email. Those clicks show up in your overall metric reporting. Depending on how the robots are configured and installed, the severity of this can range from negligible to “oh my gosh, what on earth happened here?!?!?”
| Note: The Author of this blog post, Paul Christmann (Rasa.io) will be leading a discussion on this topic during the OI-members-only Live Zoom on Thursday, January 18, 2024. OI members — see you there! Not a member? Join today — or reach out to Jeanne, our general manager, to learn more. |
Why do these computer programs exist in the first place? What purpose are they serving BESIDES making my life as an email sender harder? In short: they exist to try and make the email world safer for the end reader. Consider the history of “phishing” emails as a story of the ongoing battle between spammers and mailbox providers.
- First, spammers discover they can go phishing!
- Providers start catching words and phrases to send the mail to spam and protect the readers.
- Spammers dress up the email and add links to “real-looking” websites that try to steal credentials.
- Providers start looking for these phishing links in the emails, and again get the mail routed to spam.
- Spammers start using link shortening services to hide the bad links and fool the providers
- Providers resolve the short links (generating a click) to figure out what the link really is. Most consumer providers (Gmail, Microsoft Outlook, Apple Mail) have their own programs. Business providers often license and use products like Barracuda Email Protection or Microsoft Defender
And there we have it – the well-intentioned spam-protection service has followed a link in your email, generating a click in your reporting. The tracking and reporting service does exactly what it was asked to do: record the interaction as a click and respond with the real URL. In this case, the URL is returned to the querying bot program, which analyzes the result and decides what to do with the email but never visits the site.
How big is this?
As with many hard questions in life, the answer is “it depends”. The biggest question to ask is “Does the mailbox provider you are sending to think that your email may bespam?” If the answer to that question is “Yes”, then you are at risk of seeing larger amounts of bot-clicks.
It is important to recognize that this is different than the saying the email provider thinks your email IS spam. The provider may have questions about it, evaluate it, and then decide it is not spam and route it to the inbox. Or the provider may think it is spam without any further evaluation, and route it to the spam folder without generating any clicks at all.
Case Study: Sending Domain Change
A client changed their sending domain to a brand-new, never been warmed up but fully authenticated domain. Here is a graph representing just their bot-generated clicks over the course of 4 sends.
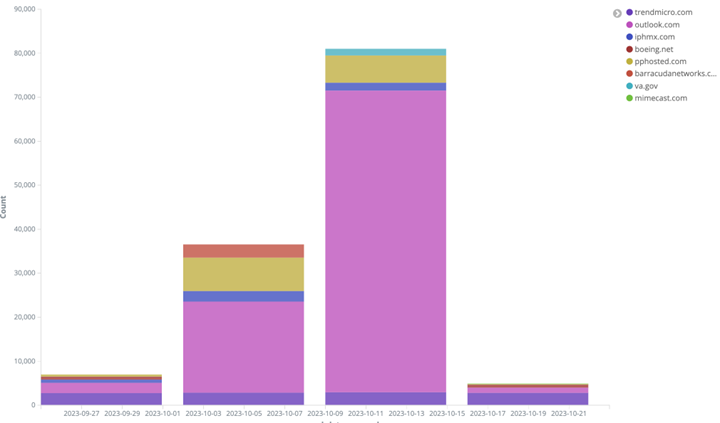
At steady state, they generally average around 10,000 bot clicks per send. On the 2 sends after they sent with a brand-new domain, the bot clicks skyrocketed to a peak of 90,000, before returning to steady state levels.
The rapid return to steady state levels along with steady “non-bot” clicks suggest that after 2 weeks of sends, the Microsoft detection services reached a conclusion that the email from this new sending domain could be trusted, and no longer needed the same level of evaluation.
This case illustrates two important points about the volume of bot clicks that might exist in your data:
- Know your steady state: This client normally receives around 5,000 “valid” clicks a day. At steady state, their bot-click traffic represented a doubling of their “real clicks”. That is their norm, and what they expected to see. Consider this in your email metrics – even when everything appears steady and normal, are you seeing what you expect to see?
- Isolating bot clicks in analytics: The impact of a change in the email ecosystem can be massive. In 2 weeks, the click volume rose by an order of magnitude and then disappeared. This leads to the “What on earth did we do right? Or wrong?” By isolating these clicks in analytics, we could observe a normal volume of clicks, indicating that overall deliverability and engagement remained the same.
Why should you care?
All day, every day: these bot-clicks are in your analytics. Maybe you have tools or an ESP that is automatically filtering them out already. Or not. Most likely – if you don’t know the answer to that question for the tool you are using, then the bot-clicks are hidden in the analytics.
This means that if you are looking at any click-based metric (clicks, unique clicks, clickthrough-rate), your stats are going to be inflated. If the actual value of the metric is important (you get paid by the click, or you pay by the click), this can become very important as revenue numbers can change drastically and unexpectedly. If, you are using the relative value of the metric to track changes in your campaign performance, you may see things that don’t exist (“We are getting so much more engagement from our audience”) or miss seeing important changes (“Delivery remains good, as our clicks are still really high.”)
What can you do?
If your ESP gives you the ability to report with and without these clicks in your data, take advantage of it. Both views give you different perspectives on the performance of your campaign, don’t rely only on one or the other view.
If your ESP doesn’t provide that ability, what can you do to spot these kinds of clicks in your data? There are a number of different heuristics you can use, including:
- Inspecting IP addresses. Some services, such as Barracuda, publicize the IP addresses that generate their clicks. You may be able to identify whether clicks originated from a cloud hosting provider rather than an end user.
- Inspecting User Agents. Some services will identify their traffic with specific user agents. Many, though, use User Agents that look real.
We have found the timing of click traffic to be a clear indicator of whether a click originated from a human or a bot. Many bot providers will scan emails and generate clicks on all of the links within a split second. This chart shows the inbound click count by second for the client referenced above. Within 30 seconds after the send of the email, inbound clicks were arriving at a rate of approximately 1000 per second. This spike tailed off rapidly, and within 4 minutes of the delivery clicks were back to “normal”. That rapid pace of traffic is a clue that something is generating traffic (even though we would all LOVE to believe that our readers respond that quickly to our emails, the reality is they aren’t THAT quick!)

Summary
Knowing about these types of clicks, you should be ready to dig deeper into your analytics and make sure you can differentiate real clicks from bot-clicks and get a more accurate picture of the performance of your email campaigns. Happy Reporting!
Read More
Image generated via AI using text prompt “The Bot Menace: Deciphering the Hidden Threat to Email Campaign Success” in Adobe Firefly.